
The writer is prooV’s VP R&D
I know PoCs – having managed several complex proof-of-concepts myself. I know that when turning to new technology, one needs to be open-minded and not held back by fear for the good ol’ legacy system, but also thorough and meticulously careful not to expose it to attacks or leak data involuntarily – with potentially devastating consequences.
In short, several powerful contradictory forces need to be balanced during every proof-of-concept, as known by all the actors of such a process – and especially information security officers.
Chief Information Security Officers (CISO) are often introduced (too) late in the process by tech companies developing solutions in the technology adoption and PoC space. By the time a new technology lands on a CISO’s desk, it has already gone through extensive evaluations.
The question on the CISO’s mind is therefore not whether the vendor’s business is stable or if the solution is technologically advanced enough to provide the desired value. Instead, the CISO needs to determine whether it is safe to integrate that technology into the company’s existing systems, and if the company will stay fully compliant with data regulations — and if all seems well, how to integrate it securely.
All of those processes involve technological challenges and frustrations of their own, so when it comes to the entire flow of introducing new technology into a large organization, CISOs are stuck between a rock and a hard place.
Safeguarding the System
The final act of a PoC, the first real-life interaction between a new technology and the legacy system is unpredictable. They might mesh perfectly on the first try, or certain adjustments will be necessary. While in some cases the new technology is outright unadaptable to the system – posing a serious threat to the organization and/or cannot guarantee the safe handling of the organization’s data.
Threats abound – it can be an open-source code used at any stage of development, or simply a fabulous new technology that wreaks havoc on the old, vulnerable legacy system. ProoV’s PoC-as-a-software platform relieves organizations from the tensions posed by the newcomer solution by testing it against a lifelike, deep mirrored copy of the original system, taking most of the weight off the shoulders of data security officers.
But what with the actual release of the new solution into the system of a large organization – packed with confidential data, closely guarded intellectual property and delicate, well-oiled processes?
Ending the PoC on a Safe Note
Running a PoC that is isolated from the corporate environment is a necessary precaution to minimize the risk of exposure and possible attacks. On the other hand, that also means that the release of the new software on the legacy system will still carry enough risk for a large organization.
To go about this many organizations set up a sandbox environment pre-release, to double-check the behavior of the new software. This solution, of course, might bring some peace of mind to management – but those responsible for the safety of the data would still not get a clear picture of how the new technology impacts their existing environment.
Thanks to our clients and vendors we know how this step brings large companies to a halt, and rightfully so. So we sat down to create a next step solution, to help our partners dot their i-s and cross their t-s and end their PoC journey on a safe note.
Last-mile Evaluation Solution in a Capsule
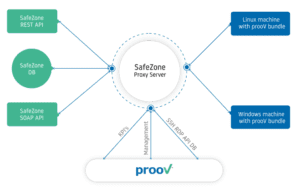
SafeZone is a unique and powerful last-mile tool, if I may say so myself. With SafeZone one could integrate the chosen vendor’s solution into the legacy system within a safe capsule, feed it obscured information (be that database or API credentials), to produce real interactions – but still keep the system safe and inaccessible outside the controlled environment of the capsule
Furthermore, SafeZone monitors and logs everything that goes on inside the capsule? And finally – after closely inspecting the ongoing processes, changes made and their effects in this semi-simulated environment – the new software can be released gradually, approving every line of code, every single action one by one.
And after all this was done and data security officers can be sure about the safety and integrity of the new technology – like a magician revealing the dove under the scarf – we could release the software by the push of a button, without going through the integration process all over again.
We thought prooV’s product range would not be complete without such a final act: a last-mile evaluation solution, that gave a fully trustworthy final answer to the question: is the new addition to my legacy system safe?
Full Access, Full Control – Line by Line
What is especially exciting for me in SafeZone, both as a prooV developer and as someone familiar with the anxieties related to a PoC is the unique access SafeZone provides during this final lap of the regulation evaluation process. Through the online prooV platform one can follow line by line, action by action all the interactions between the new tech and the company system – restricted to a safe capsule. After reviewing these lines of codes one by one, they can be tested on the legacy system, under full supervision, making sure they operate perfectly and don’t violate data regulations.
This due diligence eventually saves money, time – and gives CISOs the certainty that data was not jeopardized, systems went undamaged during the dangerous and exciting process of introducing fresh technology to the company system.